Age-verification without leaking birth date
This article describes the process of how to create a Legal Identity that can be used to demonstrate you have reached a certain age, without having to disclose your actual birth date. This is an important mechanism to protect the integrity of personal information, especially if the person is a child.
Creating a Preview ID application
The first step is to create a Preview Legal Identity application containing sufficient personal information so that the age can be verified. This application will have to contain sensitive personal information, including birth date. But creating a Preview application ensures the data is not stored in a searchable database or logs. Instead it is stored in encrypted form, and only during the process to validate the information. Once the preview application has been validated, a new application can be created, containing a subset of the sensitive information, and once that is completed, the sensitive information will be removed.
The personal data necessary to include in the Preview application is:
| Property | Description |
|---|---|
BDAY |
Birth Day |
BMONTH |
Borth Month |
BYEAR |
Birth Year |
AGEABOVE |
Age above the stated number of years |
Creating real ID application
Once the Preview application has been approved, a new, real ID application is made. This new application has to have a reference to the Preview application, and should only contain a subset of the properties. At a minimum, the following properties should be included:
| Property | Description |
|---|---|
PREVIEW |
Reference to the earlier Preview application. |
AGEABOVE |
Age above the stated number of years |
Once this application has been approved, the sensitive personal information will be removed as the preview application is deleted.
Proving your age
Proving your age is as simple as performing a Quick Login with the new identity. If property filters are used, include the AGEABOVE property. As the new identity contains a reduced set of information, and no birth-date (if it was removed in the second step above), only the AGEABOVE property is received, together with proof the Neuron has validated the claim.
How to set AGEABOVE
The AGEABOVE property should not be set to the age of the user, as that can leak personal information. Instead, it should be set to a legal limit required for one or more specific purposes. If there’s an age requirement in a country for a particular purpose, that age should be encoded in the AGEABOVE property. The property will be accepted if the personal information provided in the preview can be validated, and the age of the person deduced is at or above the indicated number.
As there are different age limits for different purposes and countries (for instance, 13, 15, 16, 17, 18, 20 and 21 are common limits), the site that tests the age of a user should not expect the number to be a specific value. Instead, it should expect the number to be at least a specific number. If there’s an age requirement for a service of 16 years of age, identities with any number for AGEABOVE greater or equal to 16 should be accepted as proof ther person is at least 16 years old.
Ensuring you have reached a certain age to create an identity
The AGEABOVE property can also be used to ensure the user of the app attempting to create an identity, has reached a certain age. Adding the property ensures the identity attempted to be created only gets approved, if the person actually has reached the age.
If the person has not reached the corresponding age, the property will become invalid, and an error with error code AgeNotReached will be logged on the application.
Validating Electronic Travel Documents & ICAO PKI Certificates
When validating electronic Travel Documents, applications need to validate against corresponding issuer certificates not managed by the operating system. To do that, the application needs to get access to these certificates somehow, and build custom X.509 chains during validation. To avoid having such an application to embed the entire list of all these issuer certificates, a list which also get regularly updated, a new repository and package is available that publishes these certificates on Neurons where the package gets installed. Applications can easily check with the corresponding neuron and download the required certificates, based on the Authority Key Identifiers available in the Electronic Travel Document certificates.
| Information about the ICAO PKI Certificate package | |
|---|---|
| Package | IcaoPkiCertificates.package |
| Installation key | vAa0l/iFHVogQYUzm+Zs6qPsw+7lYrnyFn4MNAGA7+Gso442gJJMKjknHqka/YjM6gZZSS65HL8Adbfba1067a1a27163b905869469d6f0d |
| More information | https://github.com/Trust-Anchor-Group/IcaoPkiCertificates |
#features, #id, #kyc, #neuron, #api, #repository, #package, #new
Remote Login API
Since Build 2025-12-30, extended in Build 2025-12-31, a new API called the Remote Login API is available on the TAG Neuron®. It is a complement to the Quick Login API, in the following ways:
The Quick Login API is initiated by the client itself, for instance, by scanning a QR-code, clicking a link or logging in to a web site, for instance.
The Remote Login API on the other hand, is initiated by a remote service, that wants to use the digital identity of the user in a second (or multi) factor authentication process (2FA, or MFA).
The Quick Login API allows anonymous access (on the HTTP resource level), while the Remote Login API requires authorized access. This authorized access can be granted using
WWW-Authenticateor Mutual TLS (mTLS). Mutual TLS is recommended, as it avoids the use of passwords. In both cases, the administrator of the Neuron providing access to the API needs to create a corresponding user and grant the user the corresponding privileges. (See the API documentation for details.)
Simulating Identity and Signature Petitions
A new ComSim simulation called LegalIdentities.xml simulates a series of XMPP-connected devices that apply for digital identities, and automatically respond to identity and digital signature requests. This simulation can be used for test purposes, to test function and load, as well as measure performance. It can also be used during development of other services interacting with users of digital identities for the purposes of Multi-Factor authentication. By using the digital identities of the simulated users, automatic signatures are created, which simplifies the development life-cycle, as the developer does not need to manually sign each time the MFA procedure takes place.
Report
To review the simulation model, check out the XML definition. It contains references to both the XMPP and XMPP Legal modules of ComSim. Each actor checks if they have a digital identity. If not, the actor applies for a new simple digital identity. From Build 2026-01-07 of the Neuron®, such digital identities are automatically approved. Once such approved digital identities exist, the actors stochastically send identity and signature petitions to each other. They also accept each other’s petitions automatically. This means that they will approve external requests also. This allows them to be used for other purposes as well, as mentioned earlier. You can use this simulation together with integration of the QuickLogin API and RemoteLogin API for instance.
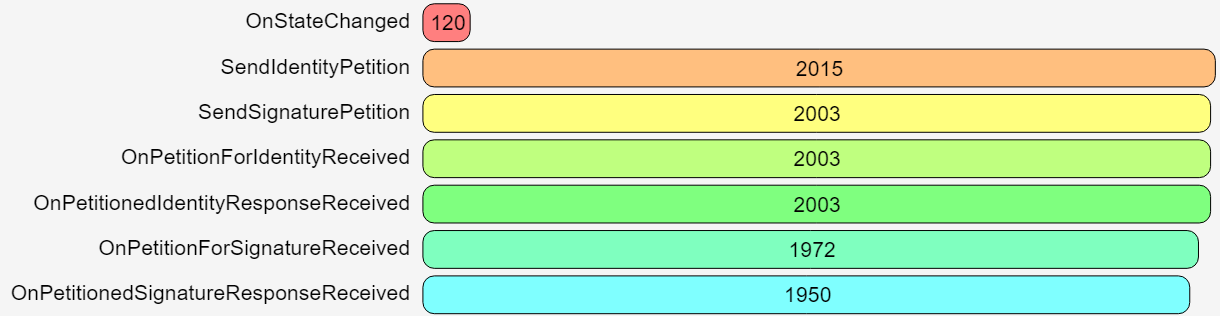
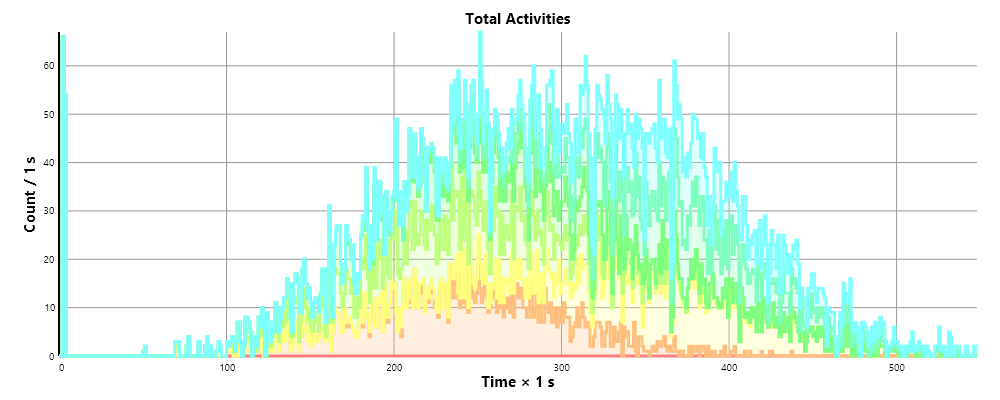
Also review the full report generated by one simulation of the model, for more information.
Resending Verification Codes during Onboarding
The TAG ID Onboarding API has been updated to allow for resending verification codes, without generating new codes. There are two parts of this API:
For clients that access an onboarding Neuron®, the
/ID/SendVerificationMessage.wsresource has been updated to allow for resending codes, by providing anResendproperty in the request. If set totrue, the resource will resend any existing code to the registered components, otherwise an error will be returned.For clients using the Agent API, a new resource is available, permitting the resending of verification codes:
/Agent/Account/ResendVerificationCodes.
Onboarding API
The /ID/SendVerificationMessage.ws now accepts payload having the following format:
{
Nr:Optional(Str(PNr like "\\+[1-9]\\d+")),
EMail:Optional(Str(PEMail like "[\\w\\d](\\w|\\d|[_\\.-][\\w\\d])*@(\\w|\\d|[\\.-][\\w\\d]+)+")),
AppName:Optional(Str(PAppName)),
Language:Optional(Str(PLanguage)),
Resend:Optional(Bool(PResend))
}
If the Resend property is available, and is true, the method will resend any existing code to the existing number or e-mail address provided. It is not possible to send an existing code to a new number or e-mail address.
Agent API
The Agent API (from build 2025-06-02) now has a new resource: /Agent/Account/ResendVerificationCodes. This resource allows for the resending of verification codes for the account currently being created. In order to access it, the JSON Web Token (JWT) provided in the response when creating the resource must be provided. The caller also needs to provide the phone number and/or e-mail address to which codes should be resent.
Security Notice: It is not possible to resend codes for accounts, numbers or e-mail addresses that have been verified. You can only resend codes for accounts still pending verification. This includes partially verified accounts. If the phone number has been verified, but the e-mail address has not, or vice versa, you can resend the code for the unverified part, but not for the verified part. Attempting to resend codes that have been verified, will be flagged, and repetetive calls to resend codes for verified accounts, numbers or addresses may result in the temporary and then permanent blocking of the endpoint making the call.
#new, #api, #onboarding, #id
Posts tagged #id
No more posts with the given tag could be found. You can go back to the main view by selecting Home in the menu above.